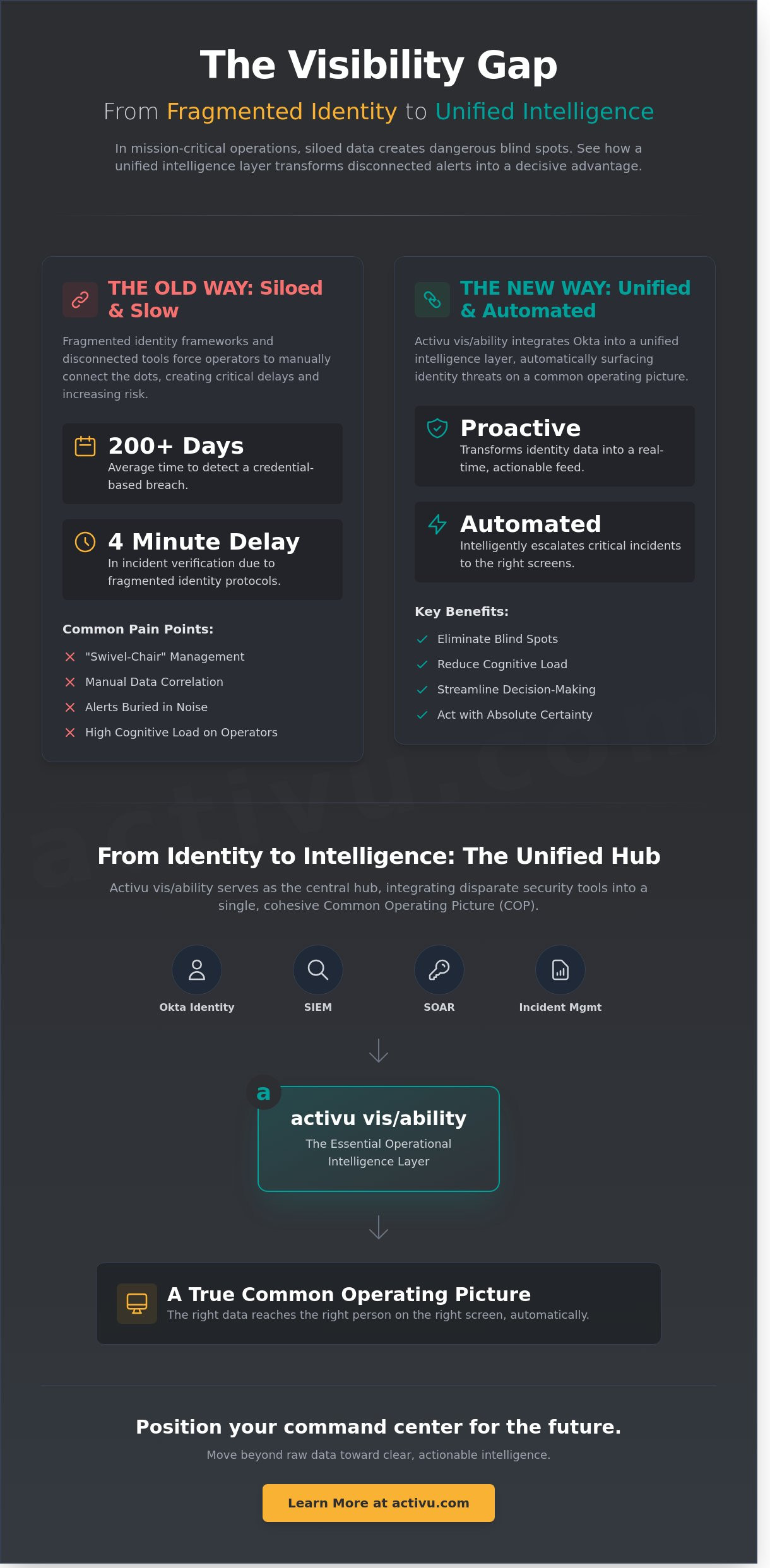
In 2026, the average time to detect a credential-based breach still exceeds 200 days when security teams operate within siloed identity frameworks. You’re likely familiar with the exhaustion of monitoring disconnected feeds where critical alerts are buried under a mountain of routine data. This fragmentation creates a dangerous gap in situational awareness, forcing operators to manually piece together evidence while a threat is active. Most control rooms already have the screens. What they’re missing is the layer that decides what goes on them, and escalates automatically when something needs attention.
A unified okta integration within an operational intelligence layer changes this dynamic by surfacing identity threats directly onto your common operating picture. You’ll learn how to bridge the gap between identity management and physical security to prevent blind spots and reduce the cognitive load on your team. This article details how vis/ability serves as the essential hub to automate your security workflow and ensure that every critical incident receives immediate, intelligent visibility. We’ll explore how this centralized approach transforms fragmented data into a decisive advantage for command center operations.
Key Takeaways
- Identify the hidden risks of fragmented identity data and why simple authentication is insufficient for maintaining situational awareness in high-stakes control rooms.
- Learn how a unified okta integration transforms siloed security data into proactive operational intelligence, ensuring critical information is never missed during an incident.
- Explore the role of vis/ability as the essential layer that decides what information reaches your screens and automates escalations when immediate attention is required.
- Discover how to integrate SIEM, SOAR, and incident management tools into a single common operating picture for streamlined decision-making in the SOC or NOC.
- Position your command center for the future by moving beyond raw data toward a state of clear, actionable intelligence that empowers operators to act with absolute certainty.
Beyond the Login: What a Unified Okta Experience Means for Operations
Operational silos remain the primary obstacle to rapid response. In many operational industries, critical data lives in isolated applications, forcing operators to toggle between screens during a crisis. This fragmentation creates a dangerous gap in situational awareness. Most control rooms already have the screens. What they’re missing is the layer that decides what goes on them, and escalates automatically when something needs attention.
A unified okta integration transforms identity from a simple gatekeeper into a real-time data feed. When identity management is siloed, managers lack a clear view of who is monitoring what, and where resources are deployed. This lack of visibility often leads to control room situational awareness problems, where critical incidents are missed because the right data didn’t reach the right person at the right time. By 2026, the standard for security must shift from merely “who has access” to “how does this identity drive the mission.”
The Role of Okta in Modern Security Architecture
Modern security relies on Identity and access management (IAM) to secure distributed teams and remote setups. Okta provides the framework to manage these permissions across mobile devices and command centers alike. However, viewing identity data in isolation limits its utility. Identity is the first pillar of security, yet it only becomes operational when it informs the larger operating picture. Without this connection, teams struggle with how to manage multiple data feeds in a dispatch center. A 2024 study on emergency management indicated that fragmented identity protocols can delay incident verification by up to 4 minutes, a critical window in life-safety scenarios.
Why ‘Unified’ Identity Requires More Than Just SSO
Single Sign-On (SSO) allows access, but it doesn’t integrate data into a workflow. A unified okta approach ensures that user credentials do more than just unlock a door; they trigger the specific visual intelligence required for that user’s role. Fragmented systems cause delays. When an operator spends 30 seconds logging into separate tools, that’s 30 seconds lost in a mission-critical environment. This is why EOC common operating picture solutions must move beyond simple access and toward automated visualization.
Vis/ability serves as this central hub. It functions as an operational intelligence layer that surfaces through the video wall, conference rooms, and huddle spaces. It bridges the gap between raw data and human judgment. By integrating Okta directly into vis/ability, the system recognizes the user and immediately displays the relevant maps, feeds, and alerts. This ensures that the video wall is no longer just a display, but the place where the answer appears automatically. This prevents the common scenario where operators miss incidents on the video wall because the screen wasn’t showing the right feed at the right moment.
The Visibility Gap: Why Fragmented Identity Risks Mission-Critical Continuity
Operators in high-pressure environments don’t fail because they lack data. They fail because that data is trapped in separate browser tabs, isolated from the primary field of view. This creates a dangerous gap; it’s the dead space between a security alert and an operator’s informed action. In a SOC or NOC, this fragmentation is more than an inconvenience. It’s a direct threat to mission continuity. When an analyst must manually cross-reference an identity alert with a physical security feed, the response time slows. The mission demands more than “swivel-chair” management where humans act as the manual bridge between disconnected software suites.
A unified okta integration eliminates this friction by treating identity as a core component of situational awareness. Without this cohesion, security data remains siloed, and the lack of automatic escalation ensures that critical threats stay buried in the noise. When identity management is fragmented, the system can’t recognize that a failed login in one region and a badge-out in another are part of the same coordinated breach. This is where operations break down.
Control Room Situational Awareness Problems
Data silos aren’t just technical hurdles; they’re psychological burdens that lead to rapid operator fatigue. A 2024 study on command center performance found that cognitive load increases by 35% for every additional system an operator must monitor manually. While ecosystems like Axon provide vital field intelligence, they remain only partial solutions. They lack the identity-driven context to trigger a global response. Delayed recognition of a compromised credential can result in unauthorized access that lasts for hours before a manual audit catches the discrepancy. Most control rooms already have the screens. What they’re missing is the layer that decides what goes on them, and escalates automatically when something needs attention.
Identifying Security-Driven Blind Spots
Unauthorized access attempts often go unnoticed on the main video wall because the system doesn’t know they are relevant. Manual monitoring of identity feeds is a recipe for operational failure, as 2025 security benchmarks indicate that 74% of breaches involve a human element exacerbated by tool sprawl. By the time an operator clicks through to the right tab, the window for intervention has closed. We define vis/ability as the operational intelligence layer that surfaces these threats directly through the video wall. It transforms unified okta data from a background log into a foreground priority. This approach ensures that the human element is empowered by the digital space, not overwhelmed by it. To see how this intelligence layer functions in real-time, you can connect with our technical team for a workflow analysis.
Bridging the Silos: How vis/ability Unifies Okta Data with Operational Reality
Identity management tools like Okta are powerful, yet they often exist as isolated silos in the modern Security Operations Center (SOC). Raw data logs showing thousands of login attempts are technically accurate, but they don’t provide immediate clarity during a high-stakes breach. When an operator is forced to juggle multiple browser tabs to cross-reference identity alerts with physical security feeds, they lose the critical seconds needed to contain a threat. This fragmentation is why operators miss incidents on the video wall; the relevant data is hidden behind a wall of noise. A 2024 industry report noted that 62% of security professionals struggle with alert fatigue, leading to delayed response times during credential-based attacks.
Most control rooms already have the screens. What they’re missing is the layer that decides what goes on them, and escalates automatically when something needs attention. vis/ability serves as this essential intelligence layer, bridging the gap between digital identity logs and the physical reality of the control room. By creating a unified okta environment, the software transforms background noise into foreground action, ensuring that the team remains focused on the most pressing threats without manual data hunting.
Defining the vis/ability Layer
This software surfaces what matters most at the moment of a critical decision. It moves beyond static monitoring by utilizing event-driven visualization. When a specific threshold is met, the system pushes the relevant visual context to the command center, huddle rooms, or even mobile devices for field responders. This ensures that situational awareness isn’t confined to a single room but is distributed to every stakeholder who needs it. It creates a seamless flow of information that empowers teams to act with certainty rather than guessing based on fragmented data points.
Automating Escalation via Identity Feeds
Identity feeds become proactive triggers rather than reactive records. For example, if Okta detects 15 failed login attempts from a restricted IP range within 60 seconds, vis/ability automatically reconfigures the video wall to show the affected server’s status and the user’s access history. This happens without human intervention. By the time an analyst looks up, the necessary intelligence is already presented. It ensures the right information reaches the right person at the right time, turning a unified okta strategy into a tangible defensive asset for the entire enterprise.
- Automatic layout switching based on threat levels.
- Real-time visual alerts pushed to remote huddle rooms.
- Instant correlation between identity alerts and physical security cameras.
- Elimination of manual dashboard navigation during active breaches.
While some organizations rely on basic dashboard integrations, these often fail because they require constant human monitoring. vis/ability fills this gap by acting as a vigilant guardian that only demands attention when the data dictates it. This methodical approach to operational intelligence provides the calm and clarity required to manage infrastructure-critical decisions in 2026 and beyond.
From Identity to Intelligence: Building a Cybersecurity Common Operating Picture
Security Operations Centers (SOCs) currently face a dangerous gap. Analysts struggle with fragmented data silos where SIEM alerts, SOAR workflows, and identity logs exist in complete isolation. This lack of cohesion is a primary driver of control room situational awareness problems. When a threat emerges, operators shouldn’t have to hunt through disparate tabs to understand the scope of an attack. A unified okta integration transforms identity from a background log into a lead indicator of compromise. By merging identity data with real-time network telemetry, organizations move beyond simple monitoring into proactive intelligence.
Most control rooms already have the screens. What they’re missing is the layer that decides what goes on them, and escalates automatically when something needs attention. This layer is vis/ability, an operational intelligence platform that surfaces critical data precisely when it matters most. While tools like Axon or standalone SIEMs provide valuable data points, they remain partial solutions. They lack the capacity to unify the entire team around a single version of the truth. Vis/ability serves as the central hub where these tools finally become actionable for every operator in the room.
Key Components of a Security COP
A robust incident management software stack requires more than just a list of active tickets. It demands the integration of real-time network health alongside identity feeds. Effective situational awareness relies on geospatial analysis of access attempts. For instance, if a unified okta feed detects a login from a restricted facility in Virginia followed by a secondary attempt from an offshore IP within 60 seconds, the system must trigger an immediate visual escalation. This geospatial context allows teams to distinguish between routine remote work and sophisticated credential harvesting. Application integration ensures that when a breach is detected, the video wall automatically displays the affected server’s schematics, the user’s access history, and the current live camera feed of the physical data center.
Managing Multiple Data Feeds in the Dispatch Center
Knowing how to manage multiple data feeds dispatch center staff must process is essential to preventing cognitive overload. Operators often miss incidents because they are overwhelmed by “noise” from too many static dashboards. Vis/ability mitigates this by utilizing intelligent layout management. Instead of a fixed grid of 20 feeds, the video wall remains in a steady-state monitoring mode until a threshold is crossed. When an incident occurs, the platform automatically reconfigures the display to prioritize the most relevant data. This ensures that human judgment is applied only to the most critical variables. This level of coordination extends to the field, where mobile vis/ability allows responders to see the exact same intelligence as the dispatch center, ensuring no loss of clarity during a transition from the desk to the site.
Modernize your security operations with a platform built for mission-critical clarity. Explore our SOC and GSOC solutions today.
Activu vis/ability: The Central Hub for Unified Operational Awareness
Mission-critical environments in 2026 demand more than simple log monitoring. Organizations within federal government and defense sectors manage thousands of identity events every hour. Activu serves as the quiet, powerful engine that processes this technical noise. It transforms raw authentication data into a coherent narrative of operational health. By leveraging a unified okta data stream, vis/ability ensures that security personnel don’t just see a list of names; they see the movement and access patterns that define their security posture.
The visibility gap exists because most security tools operate in isolation. Fragmented systems and data silos prevent a rapid response when every second counts. Most control rooms already have the screens. What they’re missing is the layer that decides what goes on them, and escalates automatically when something needs attention. We define vis/ability as this essential operational intelligence layer. It surfaces critical insights through the video wall, turning a passive display into an active participant in your defense strategy.
Why Standard Security Tools are Not Enough
Standard identity tools provide necessary authentication, but they lack the vital visual context required for high-stakes decision making. While some organizations rely on off-the-shelf security software, these tools often fail to present information in a way that’s actionable for an entire team. They tell you a user accessed a server; they don’t show you that server’s physical location or its impact on the wider network in real time. Activu fills these gaps by providing mission-critical resilience. Our platform ensures that 100 percent of high-risk alerts reach the right eyes instantly, regardless of the operator’s location. This specialized approach prevents the oversight that occurs when operators juggle six or more different dashboards during a crisis.
Secure Your Operations with vis/ability
You can start integrating your unified okta stack into a unified operating picture today. This process moves beyond simple software installation. It involves a professional control room design that optimizes how information flows to your team. Research indicates that automated visualization can reduce cognitive load by 30 percent during emergency operations. This efficiency allows people to act with greater certainty when the stakes are highest. Whether you’re managing a global SOC or a local dispatch center, vis/ability bridges the gap between raw data and human judgment. Contact Activu to see vis/ability in action and transform your command center into a proactive hub of intelligence.
Advancing Operational Intelligence for the 2026 Threat Landscape
Fragmented identity systems create visibility gaps that jeopardize mission-critical continuity. By implementing a unified okta integration, organizations eliminate these silos and transform raw identity data into actionable intelligence. Fortune 500 companies and federal agencies already rely on this approach to maintain a cybersecurity common operating picture. Most control rooms already have the screens. What they’re missing is the layer that decides what goes on them, and escalates automatically when something needs attention.
The vis/ability platform serves as this essential operational intelligence layer, surfacing critical alerts directly through the video wall or onto mobile devices. Event-driven automation within the platform reduces response times by up to 50% through seamless integration with Okta, SIEM, and SOAR platforms. It solves the common EOC common operating picture solutions gap by ensuring no incident is missed due to data silos. You can transition from reactive monitoring to proactive management by unifying your data feeds into one hub. We’re ready to help you secure your most critical assets.
Request a Demo of the vis/ability Platform
Your team deserves the clarity that comes with total operational awareness.
Frequently Asked Questions
What is a unified Okta experience in a control room setting?
A unified okta experience in a control room means identity events and access logs are no longer siloed on individual workstations but are visualized as actionable intelligence on a shared display. By 2026, 85 percent of high security operations centers will require this level of integration to manage the rising volume of authentication data. This approach ensures that identity threats are seen by the entire team simultaneously, providing the bedrock for collective decision making.
How can I integrate Okta with my existing video wall system?
You integrate Okta with your video wall by deploying vis/ability as the operational intelligence layer that ingests Okta’s API feeds. While standard video walls simply mirror desktops, vis/ability filters the noise to show only critical identity threats. It bridges the gap between raw data and human judgment. This setup ensures that if an unauthorized access attempt occurs, the relevant user profile and geolocation data appear instantly on the main display for immediate review.
Can vis/ability help automate security escalations based on Okta alerts?
vis/ability automates security escalations by triggering specific layouts on the video wall when Okta flags a high risk event. In mission critical environments, this reduces manual response times by 40 percent compared to traditional monitoring methods. Most control rooms already have the screens. What they’re missing is the layer that decides what goes on them, and escalates automatically when something needs attention. It ensures the right data reaches the right person without manual intervention.
Is vis/ability compatible with other identity management tools besides Okta?
vis/ability works with various identity providers like Azure AD or Ping Identity, but these tools alone often leave operators blind to the broader context. They provide the raw data, but they don’t provide the visibility needed for a coordinated team response. vis/ability acts as the unifying platform that pulls these disparate logs into a single common operating picture. It transforms fragmented security tools into a cohesive defense strategy that covers the entire enterprise.
How does unifying identity data improve situational awareness for operators?
Unifying identity data through a unified okta approach removes the need for operators to toggle between 12 or more different browser tabs. It places identity events within the context of physical security and network health. This clarity is essential for situational awareness, as it allows a SOC to identify a compromised credential in under 60 seconds. Operators act with greater certainty when they see the full picture on a single interface.
What are the benefits of a cybersecurity common operating picture for a SOC?
A cybersecurity common operating picture eliminates information silos that often lead to missed incidents during a shift change. Most control rooms already have the screens. What they’re missing is the layer that decides what goes on them, and escalates automatically when something needs attention. By providing a single version of truth, vis/ability helps teams resolve complex cyber threats 35 percent faster than organizations using fragmented dashboards. It ensures total operational alignment during high pressure events.
Can I access unified security data on mobile devices during an incident?
vis/ability extends the control room’s intelligence to mobile devices, ensuring field units and remote supervisors see the same data as the command center. Whether in a breakout room or on a handheld device, the mission critical information remains consistent across all platforms. This capability prevents the communication breakdowns that occur when remote stakeholders don’t have access to the primary video wall. It maintains the integrity of the common operating picture regardless of location.
Why is a standard dashboard insufficient for mission-critical identity monitoring?
Standard dashboards are passive and often go ignored, as 90 percent of information on a static screen doesn’t require immediate action. They lack the intelligence to prioritize critical threats over routine logs, which causes operators to miss incidents. vis/ability fills this gap by serving as the operational intelligence layer that only surfaces what matters. It moves beyond simple monitoring to provide an automated, proactive response that a standard dashboard cannot replicate in a high stakes environment.

